Recently Apple was hit with two big issues in the same month. These gave rise to concerns that Apple products might not be as secure as most think. The first of the two came in the form of a text message that can be sent to Apple iPhones.
The text, which is entirely in Arabic, can be sent to anyone with an iPhone, and it will immediately shut down the phone. While this is more of an annoying bug than a security concern (although it definitely can be viewed as a security concern, depending on the owner of the phone and his/her need for uptime), it doesn’t seem to be harmful to the devices. Users in the Reddit.com forums found the bug, and it appears they did so by accident.

Credit: parts of this image are reproduced with permission from: https://commons.wikimedia.org/wiki/File:Unibody_Macbook.JPG.
If your phone receives the dreaded text message, you will need to turn on your phone and delete that message. One workaround to the text issue is to go into the settings,and turn off text message previews that appear on the home screen. Apple is aware of the bug and will resolve the issue in its latest update, which should be coming very soon.
The second security concern, and one that is very critical to businesses is the latest exploit which allows someone to put a permanent backdoor onto your Mac by rewriting the firmware for the BIOS to allow remote connection to the device. This affects all Macs older than mid-2014.
The reason this security concern is so troubling is, unlike other types of exploits, where if you were to be hacked you could wipe your hard drive and start clean with the appropriate updates, this targets the BIOS, meaning no matter how often you wipe your hard drive, hackers can exploit the vulnerability over and over again.
The vulnerability can be enacted as soon as a machine is woken from Sleep Mode. The security researcher who found the exploit, Pedro Vilaca, stated you can stop your machine from going into Sleep Mode to bypass the exploit. However, Apple is aware of the exploit and should patch it soon. Vilaca also stated that this is very similar to last year’s “Thunderstrike Proof-of-Concept” exploit.
While nothing will protect against this current exploit (i.e. antivirus, anti-malware), it does show that as Macs become more popular, holes are being found in the OS and, in this case, in the hardware itself. Business owners must be aware of both where their employees go on the Internet and how to protect their assets from hacking attempts.
Everon offers antivirus for Macs, as well as PCs, with a product called Webroot Secure Anywhere. We can assist in setting up hardware proxies that will prevent unauthorized access to the Internet. If you have any questions about what we can do for your Apple environment, feel free to call our techs at 1-888-244-1748 (or email at [email protected]). We’re here for you. Twenty-four/seven, 365.
——-
You may also like:
- How to Get iOS Devices to Work with Windows Servers
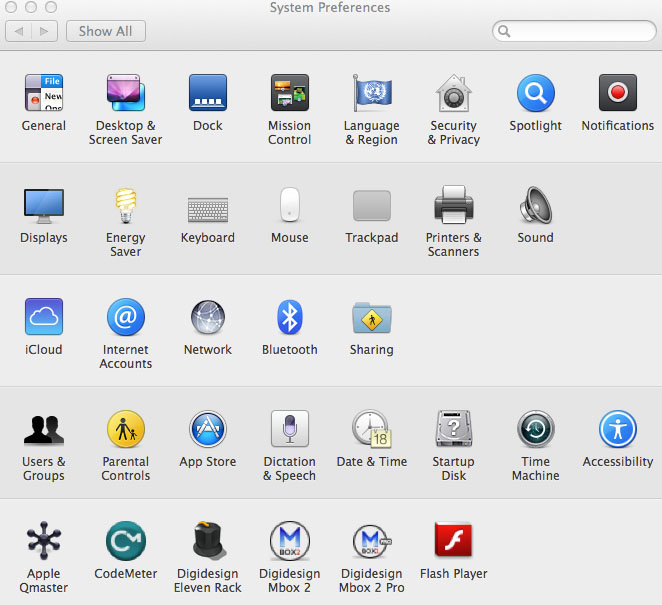
- Security on a Mac: Setting Passwords & Locking your Screen
- Now Offering Webroot Antivirus
- Is Your Backup Plan Obsolete?
- IoT SMB: The “Second Mover Benefit” for Small Business