Recently I received a complaint about an extremely slow flow on a network. I conducted various scans on the network and did packet capturing analysis only to discover a unique and unusual case that I had never encountered before. I found a major bandwidth consumption by a few files trading on the network with the extension *.drg. I conducted a full research about this specific extension and its files, discovering that the .drg file extension is used for AllyCAD CAD design drawing files, AviSys bird watcher database files, Dyno2000 car design files, VLBI and Tied Array drudge tasking document files. After contacting the client with my findings, I concluded that none of his users were using the software listed above. I ran a full software scan and analysis and discovered that three of the network users had an app called i-Doser installed on their iPhones, and they were connected through the corporate WiFi.
By now you must be wondering, “What is i-Doser?” I-Doser is an application for Windows and iOS that you can find on the Internet. It is used to achieve a simulated feeling of a “drug” through the use of binaural beats. There are well over one hundred “doses” or “dosers”, and some can be incredibly hard to find. Most of the doses are named after prohibited recreational drugs. In other words, it’s a brainwave synchronization software which is used for mood alteration purposes. The DRG files contain stereo audio tracks that are recorded using the binaural recording techniques used by the software. The DRG files also contain information about the “dose” file and a screenshot image.
I was extremely curious about i-Doser and its concept. What pushed these employees to use digital drugs in the work environment? How effective are digital drugs? Should employers be alarmed? According to research on i-Doser’s website, 83% of its users have had at least one simulated experience occur. There is substantial evidence and research to support i-Doser’s claim that binaurals can help simulate a specific mood or experience. But I was definitely a skeptic, so I decided to try this i-Doser myself. After-hours, of course.
I chose a dose called “Gates of Hades.” I looked up the reviews online for it, and what I saw creeped me out. People were saying that it was the most frightening thing they’ve ever experienced, e.g. near-death experiences, OBEs, distortion of reality, loss of body image, strong visual and auditory hallucinations… the works. But, being the skeptic that I am, I decided to ignore all the talk and reviews. I said to myself, “People are just trying to scare each other.” So last night I plugged my HD headphones into my iPhone, laid in my dark room on my bed (as was recommended, in preparation for this specific dose), and proceeded to listen to “Gates of Hades.”
 As a veteran of the United States Army, I have been deployed to combat zones and have experienced some horrifying experiences. After my experience with I-Doser, I have to admit the “Gates of Hades” dose is real, and it works.
As a veteran of the United States Army, I have been deployed to combat zones and have experienced some horrifying experiences. After my experience with I-Doser, I have to admit the “Gates of Hades” dose is real, and it works.
After I finished listening to the full dose, I experienced unusual sensations and serious anxiety that stayed with me for almost a full hour. Maximum depression-like sensations. I was seeing colors darker than what they really are. This was like a living nightmare that I was trapped in for a full hour. This dose is very dangerous and shouldn’t be traded between people, especially teenagers. The brain-experience and reaction I had was totally horrifying and accompanied by hallucinations.
The digital drugs are real, and they’re not as safe as most users claim.
After my horrifying experience with “Gates of Hades” and the reaction that I lived for a whole hour I wanted to understand more how this could possibly happen to me. I researched more in books and on the Internet about binaural beats. I found a logical, scientific explanation that I would like to share with you. Based on the Monroe Institute for Neural Science‘s research for binaural beats:
“The sensation of auditory binaural beats occurs when two coherent sounds of nearly similar frequencies are presented, one to each ear, with stereo headphones or speakers. The brain integrates the two signals, producing a sensation of a third sound called the binaural beat. For example, if a frequency of 100 Hz is played in one ear and 107 Hz is played in the other ear, a binaural beat of 7 Hz is created by the brain. Brain waves match or “follow” the binaural beat. If the binaural beat is 7 Hz, an increase in the brain waves of 7 Hz occurs. Binaural beats originate in the brainstem’s superior olivary nucleus, the site of contralateral integration of auditory input. The binaural beat is neurologically conveyed to the reticular formation which uses neurotransmitters to initiate changes in brainwave activity.
Brain Waves & Consciousness:
Gamma ( above 40 Hz ) Alert anxiety and could lead to hallucinations.
Beta ( 13 - 26 Hz ) Alert concentration and problem-solving.
Alpha ( 8 - 13 Hz) Alert relaxation.
Theta ( 4 -7 Hz) Deep relaxation and increased learning.
Delta ( 1 - 3 Hz ) Deep Sleep.”
I also discovered that the binaural beats have been used in the movie making industry since forever, recently on a more advanced level, which is known as sound effects. Have you ever asked yourself why, every time you are watching a horror or action scene there is always that super-surround, high-pitched sound effect in the background? Yes, that’s right, welcome to the Gamma Brainwave! These sound effects trigger the Gamma brainwaves causing instant fear and anxiety. Later on, you might even experience nightmares, not because of what you saw — it’s because of the high frequency rate that was triggered in your brainwaves. It usually takes time to discharge its intensity to a lower level than 40 Hz. The reaction time lapse can differ from one person to another depending on the severity of that brainwave trigger they have been exposed to.
After my firsthand experience with this digital drug, or i-Doser, I can see that the use of this program during work hours should be a concern for employers. While some employees may just be trying to de-stress, the use of any “drug” to alter their states (and possibly their judgments) is alarming.
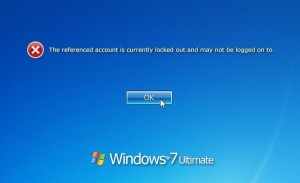
There are lots of opinions about this new i-Doser digital drugs. Some are skeptics, some are believers, and some are addicted to i-Dosing. It’s clear that these type of digital drugs should of concern in the work environment. The user must isolate himself from the surrounding environment — in other words, breaking away from the work team and allowing himself to fade into the background. This would affect the general production of any company. Further, the i-Doser application uses a very specific file extension that is dependent on on live broadcasting from different servers, which consumes a great amount of bandwidth on any network. It’s very similar to the music broadcasting software called Spotify, which most companies currently ban using the corporate firewall and the security policies on their Active Domain Servers.
The Oklahoma Bureau of Narcotics has issued numerous warnings about i-Dosing and its dangerous side effects. Some countries in Europe, such as, France have issued new laws to ban i-Dosing. U.A.E and Lebanon in the Middle East have similar bans. These countries have taken serious counter measures against this new trend of Digital Drugs. Don’t you think it’s time to stop being skeptical and realize that it’s a real threat?
If you are concerned about the possibility of digital drugs on your company’s network, please call us at Everon (888-244-1748). Our team can review your network and recommend next steps for your systems.